
Cryptolocker remains a real threat to your data.

Yesterday we saw another Cryptolocker attack. An employee innocently opened an email and inadvertently downloaded a cryptolocker virus onto his computer putting an entire network of around 40 users under threat. We were onsite within the hour to isolate the problem and managed to achieve a best case scenario of ½ a day of downtime for the business. I would hate to estimate the cost of sending around 40 employees home for this time. Had they not acted quickly it could have been much worse.....
Mondays attack resulted from a fake email from supposedly the NSW state revenue office. LOOK out for emails that typically have attachments (like a .zip or .exe), it could install CryptoLocker or other damaging infection. However recently it seems to be more common for the Cryptolocker infection particularly to be a link that the user follows. See below for an example with the link circled in RED.
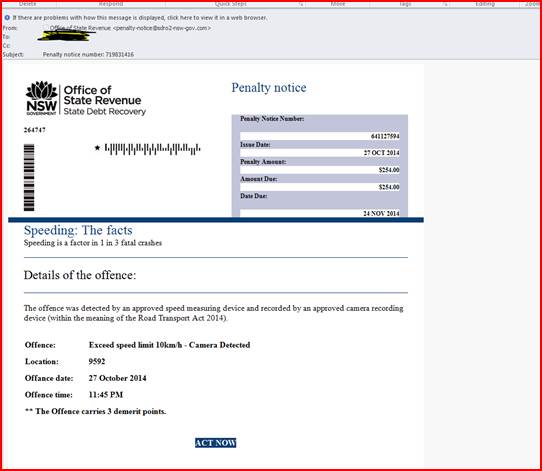
Checking the senders address is also a good way of checking. If the email is meant to be from the National Australia Bank for example, the senders address should be something like info@nab.com.au.
If the sender address is more like info@national-aust-bank.net then you can assume something isn’t right. Best thing to do is if you are not 100% sure it’s O.K, call us and will check for you and DO NOT CLICK the link.
How you can protect yourself -
- DO NOT open files attached to emails, unless you are specifically expecting to receive the files. This is particularly important for emails coming from the unknown addresses. However even emails from people you know can be fakes if they have been infected themselves.
- DO NOT click on links in emails unless you can verify that the link goes where it says it does (hover your mouse on the link, and check the actual URL in the bottom corner of the email). This especially applies to shortened links.
- The best defence is to ensure you have a current and VALID backup in place. In the event you are infected and you have a valid backup your files can be quickly retrieved, minimising downtime and interference to your work. A backup that is rotated daily with a copy kept away from the computer is best.
Whilst we can implement more complex solutions, they are usually not cost effective. To give you a solution that will protect you 100% will cost many $1000’s initially and as future threats emerge may not be effective against them, resulting in constant monitoring and improvement, again costing many $1000’s. This may be worth it for large organisations, most small to medium businesses simply cannot afford it. As the old saying goes Keep It Simple Stupid.
Contact us on 03 9874 5473 to find out more, or to assist in anyway.
« Back to News




 (03) 9874 5473
(03) 9874 5473 By Luke Smits - Founder & Operations Manager
By Luke Smits - Founder & Operations Manager